NullCon - ZONEy
- Introduction
- Enumeration
- Exploitation
Introduction
Description
Are you ZONEy.eno out or can you find the flag?
52.59.124.14:5007 (UDP)
Enumeration
Nmap
This challenge was in the web-category, but the description indicates that the server is running over UDP. HTTP runs over TCP (except for HTTP3 that runs over QUIC), so this is weird …
I decided to launch nmap on this port to see what is it all about:
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[~/ZONEy]
└─$ nmap -Pn -sC -sV -sU 52.59.124.14 -p 5007
Starting Nmap 7.95 ( https://nmap.org ) at 2025-02-02 03:04 CET
Nmap scan report for ec2-52-59-124-14.eu-central-1.compute.amazonaws.com (52.59.124.14)
Host is up (0.025s latency).
PORT STATE SERVICE VERSION
5007/udp open domain NLnet Labs NSD
Querying DNS
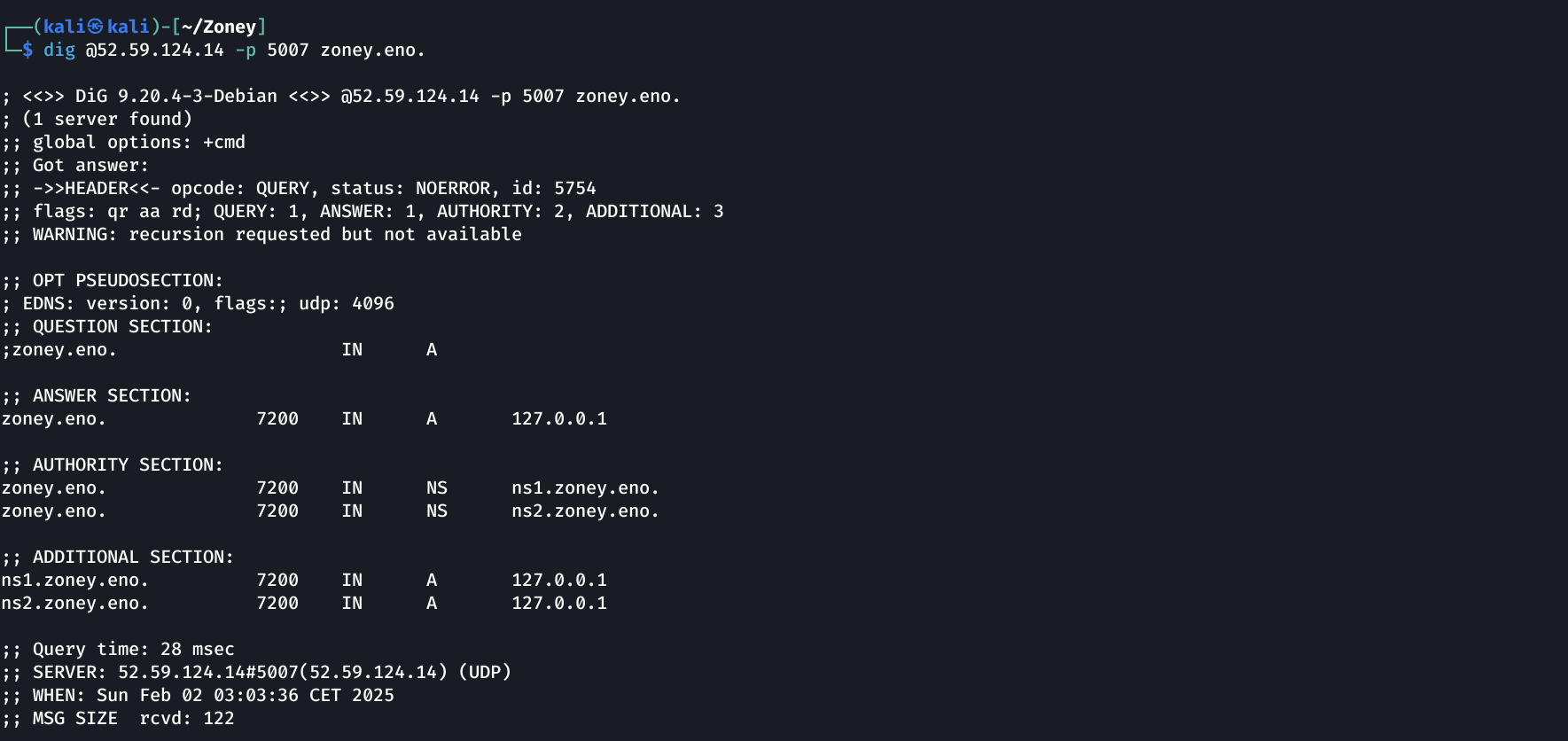
Nmap says that a DNS server is running on that port. Let’s confirm this statement using dig to query for the ZONEy.eno domain (as mentionned in the description):
1
dig @52.59.124.14 -p 5007 zoney.eno.
DNS enumeration
| Query | Found | Pointing |
|---|---|---|
Queries on a domain that is not zoney.eno |
Refused by the DNS server | N/A |
Not specifying query type on zoney.eno |
ns1.zoney.eno | 127.0.0.1 |
| ns2.zoney.eno | 127.0.0.1 | |
| hostmaster.zoney.eno | 127.0.0.1 | |
MX on zoney.eno |
challenge.zoney.eno | 127.0.0.1 |
| Subdomain bruteforcing | www.zoney.eno | CNAME on challenge |
I tried querying for TXT, CNAME and so on all theses domains but nothing interesting. I tried AXFR with every domains, still nothing.
Exploitation
DNSSEC
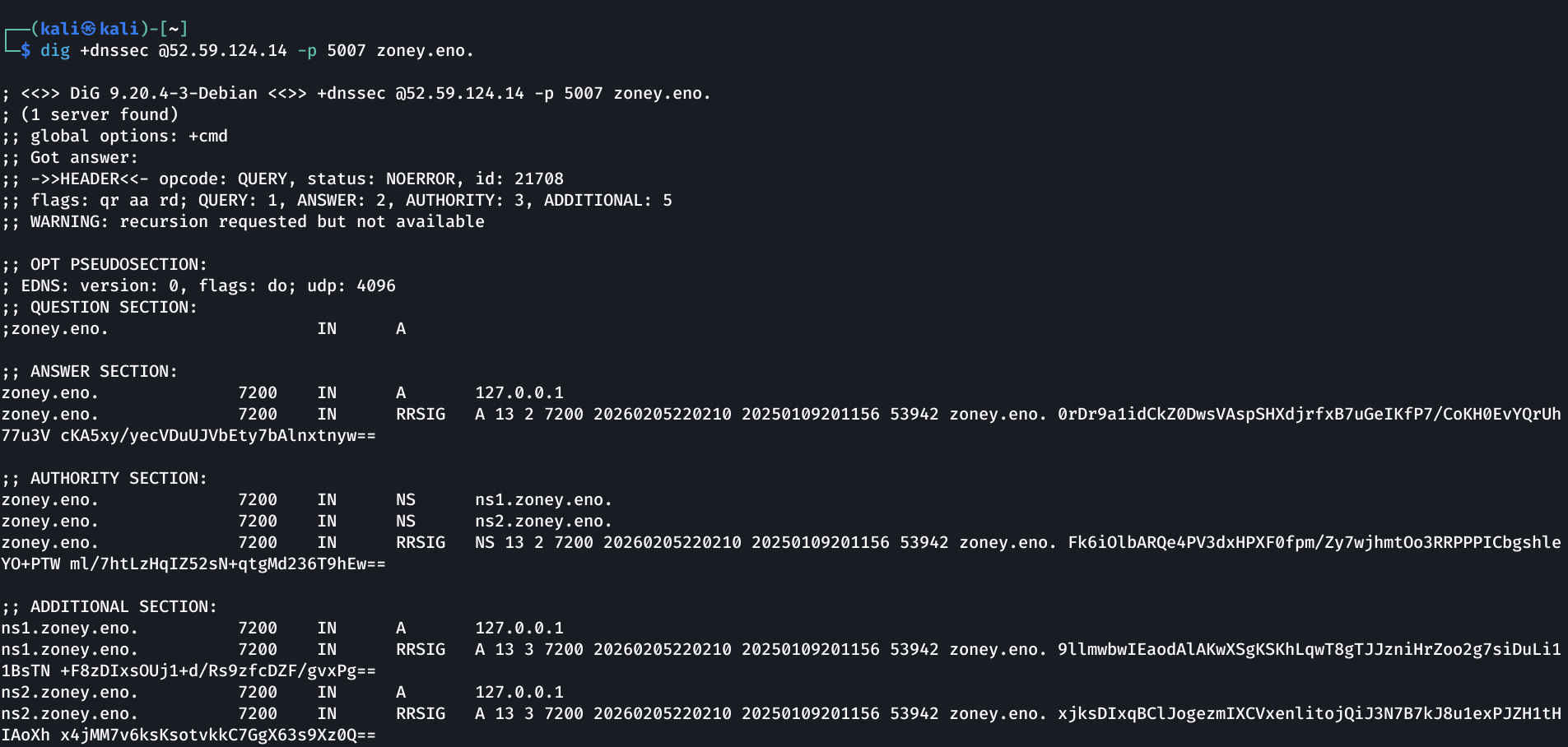
Eventually I started to enumerate DNSSEC:
1
dig +dnssec zoney.eno. @52.59.124.14 -p 5007
I thought let’s try zone walking !
Zone Walking
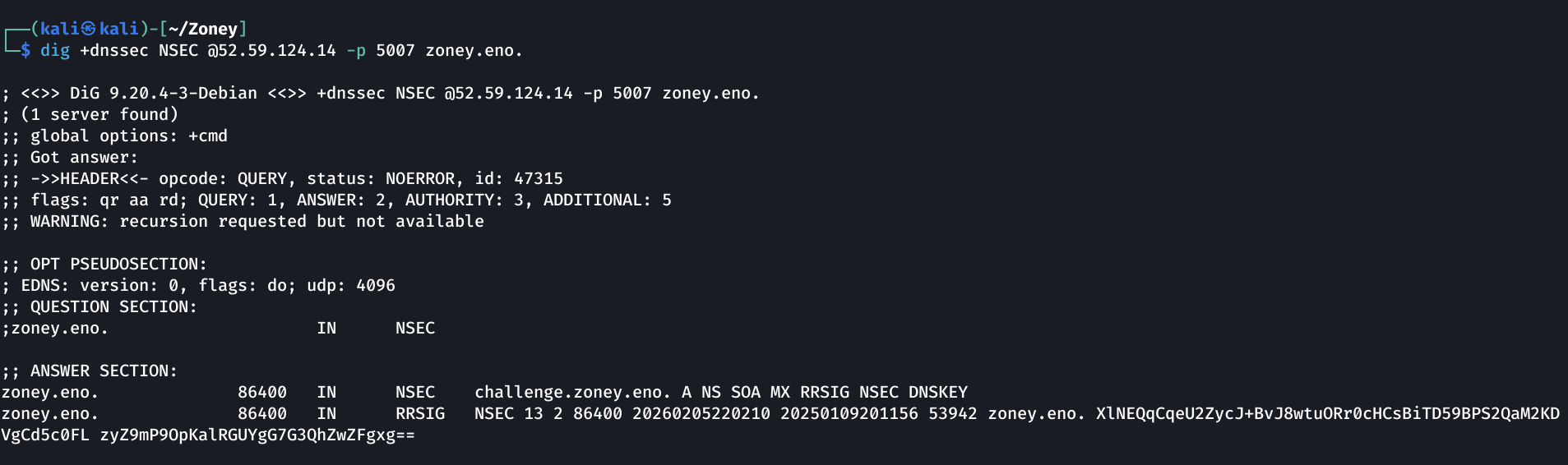
zoney.eno
1
dig +dnssec NSEC @52.59.124.14 -p 5007 zoney.eno.
We see this line on the top of the ANSWER SECTION:
1
zoney.eno. 86400 IN NSEC challenge.zoney.eno. A NS SOA MX RRSIG NSEC DNSKEY
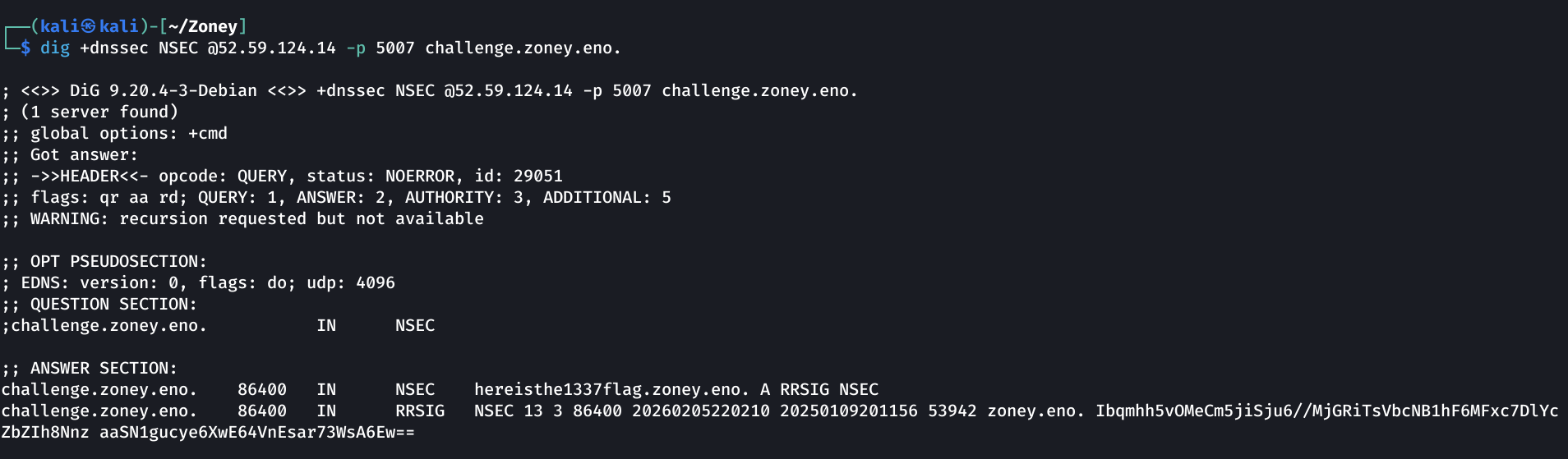
challenge.zoney.eno
1
dig +dnssec NSEC @52.59.124.14 -p 5007 challenge.zoney.eno.
We see this line on top of the ANSWER SECTION:
1
challenge.zoney.eno. 86400 IN NSEC hereisthe1337flag.zoney.eno. A RRSIG NSEC
hereisthe1337flag.zoney.eno
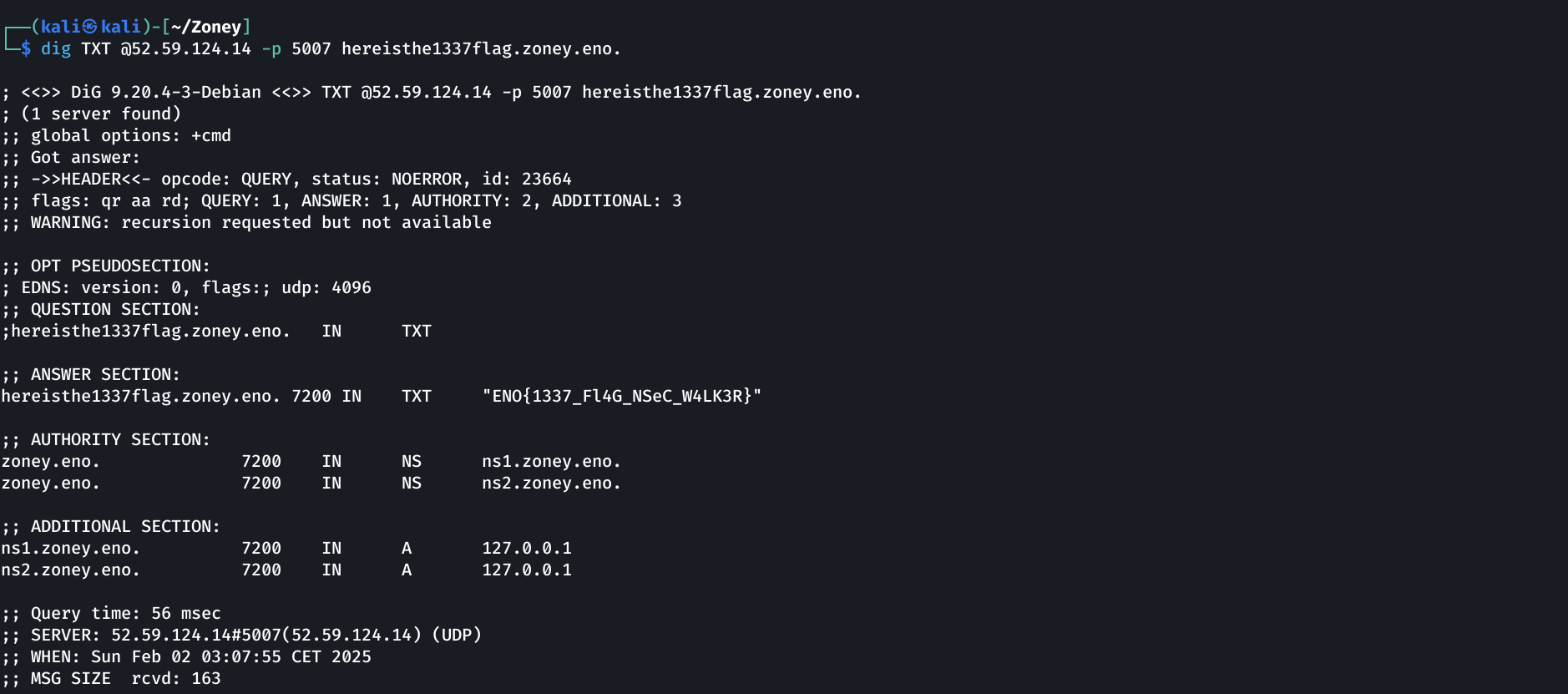
I started by querying for TXT records on this newly found domain:
1
dig TXT @52.59.124.14 -p 5007 hereisthe1337flag.zoney.eno.
Getting the flag
1
ENO{1337_Fl4G_NSeC_W4LK3R}